ProGet
ProGet 2022: What is Software Composition Analysis (SCA)?
ProGet 2022 has been released! We’ve made a lot of improvements, but some of the most exciting changes are the revamped Software Composition Analysis (SCA) features.
Not only are Vulnerability Scanning and License Detection/Blocking a lot easier to use, but they’re integrated so that you can see which of your applications are using unwanted packages. ProGet will also alert you to the packages you use that have issues like vulnerabilities.
It’s pretty easy to start using these features, and in this article, I’ll explain:
- What is Software Composition Analysis (SCA), and why you should use it
- Using “Projects and Releases” in ProGet to track package usage
- Continuous Analysis to identify issues (vulnerabilities, licenses) in your applications
- How to start using these features today
Software Composition Analysis (SCA)?
Broadly speaking, Software Composition Analysis (SCA) helps you find vulnerabilities and unwanted licenses in the open-source and third-party components that your applications use.
It’s a process that starts by identifying which third-party libraries, open-source packages, and other dependencies that your applications use. For example, your ASP.NET Web Application will have dozens of different NuGet packages like System.DirectoryServices.Protocols 5.0.0 and Newtonsoft.Json 12.0.3.
Once the packages are identified, they’re compared against a variety of databases like the National Vulnerability Database (NVD) to determine the licenses used and the known vulnerabilities. For example, if you follow the links on the example packages from above, you’ll see that both packages are MIT-licensed and have known vulnerabilities.
This list of packages – along with their licenses and vulnerabilities – can then be compiled into a standardized Software Bill of Materials (SBOM) document, and shared internally or with customers. You can then reference these SBOM documents to see which applications use which packages or vice versa.
ProGet can do all of this automatically, as well as provide you with a UI to easily find this package usage. ProGet will even proactively identify issues in packages like vulnerabilities and unwanted licenses and give your team a chance to resolve them.
This is becoming more and more important, especially as your applications consume more open-source packages, the “supply chain attacks” on these packages are rising. Having SCA integrated into your build process can be invaluable when new vulnerabilities are discovered, such as the now-infamous Log4j vulnerability.
Log4Shell and SCA
You can manually perform Software Composition Analysis on your applications by looking at lock files and build output – and a lot of teams had to do just that when the Log4j vulnerability was disclosed. It’s an extremely tedious and time-consuming process:
- Search all of your servers for applications that have files with names like
log4j-api-2.*.0.jarandlog4j-core-2.*.0.jar - Look in all code repositories that reference that library
- Dig through build logs to try to find references to log4j
- Compile a report of all of the applications that you discover through this process
- Communicate with each team to identify if the release is active or not
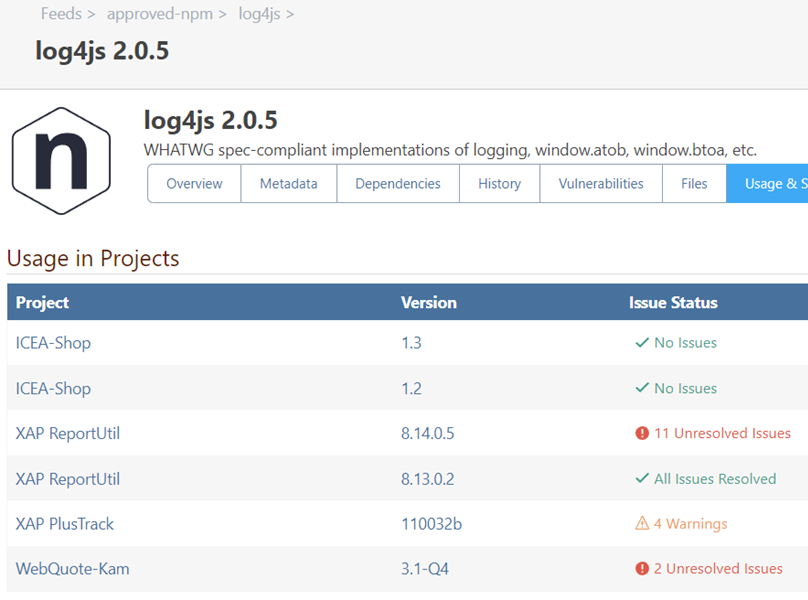
Alternatively, if this were automated, it’d simply involve navigating to ProGet and looking at the vulnerable packages to see which active applications were using it. For example, something like this:
What are Projects & Releases?
When you click on “Reporting & SCA” in the navigation, the first thing you’ll be taken to is the “Projects” tab, which is right next to the “Releases” tab. Projects and Releases are a new feature in ProGet that help you track the open-source and third-party components (packages) that your organization uses.
A project represents an application, microservice, or other software components that are built using open-source or third-party software packages. They’re intended to represent software that you deploy to servers, the cloud, customers, etc.
A release is a version of that package and is essentially where the inventory (list) of the names and specific versions of those packages are stored.

Projects, releases, and the packages they use will be automatically created when you integrate ProGet into your CI/CD pipeline, which I’ll talk about in a little bit.
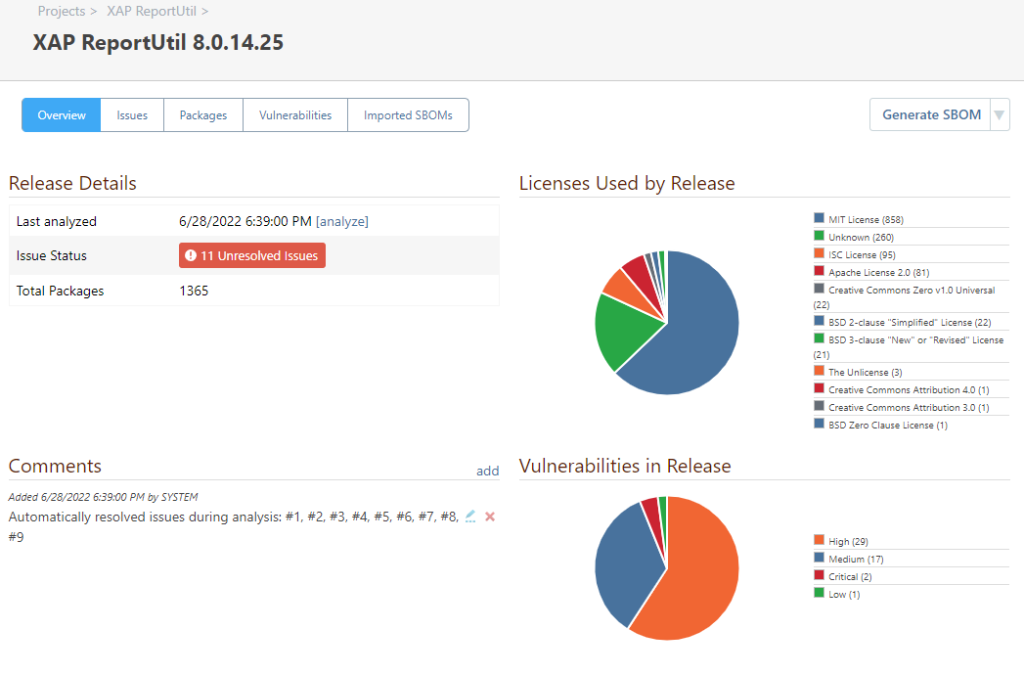
Continuous Analysis: Releases & Issues
ProGet will routinely analyze your active releases for new vulnerabilities or unwanted licenses in the packages it uses. For example:
- Missing Packages, that are not stored in ProGet but used in your applications anyways
- Vulnerable, such as those with “Severe” assessments
- Unwanted License, such as those with a GPL3 license
When ProGet detects an issue with one of those packages, then an issue will be created and the project owner will be notified. From there, the issue can be remediated or resolved.

How to start using SCA in ProGet
The best and easiest way to perform Software Composition Analysis (SCA) on your applications is during your build / Continuous Integration (CI) process. This involves running a command-line tool named pgscan after building your application.
pgscan is a free and open-source tool that will scan your just-built code, identify the open-source components that are being used, and publish that information to the ProGet server for further analysis.
How to Use the pgscan Command-line Interface (CLI)
You can install pgscan as a dotnet tool, or simply download the file from our GitHub repository.
From there, you just need to run a command like this after building:
pgscan identify
--api-key=mySecretKey1000
--proget-url=https://proget.corp.local/
--input=MyApplication.csproj
--type=nuget
--project-name="My Application"
--version=5.00.21After that, pgscan will identify the open-source components found in the application, compile a Software Bill of Materials (SBOM), and upload it to the target ProGet server. From there, you’ll be able to see all the packages that “MyApplication” uses by navigating to the “5.00.21” release.
See SCA and Continuous Integration (CI) for more guidance and instruction on how to integrate ProGet and pgscan.
