Package Management
CMPR: Signs You’re a Level 1 in Package Maturity
This article is 1/5 in our series on Centrally Managed Package Repositories, also available as a chapter in our free, downloadable eBook Package Management at Scale
Most organizations start here—but few remain at this level for long. It’s worth asking: are you here now? If what follows feels familiar, you’re likely operating at Level 1. If not, feel free to skip to the next article in the series.
At this early maturity stage, package management is unstructured and inconsistent. Developers pull third-party libraries directly from public sources like Nuget.org, npmjs.org, or PyPi. There are no internal repositories, centralized oversight, or tools to enforce standards. Teams store these in local development environments or transient CI caches and work independently, using packages based on immediate needs without coordination. When building and releasing software, teams may rely on local builds or shared CI scripts, but without controlled dependencies, results are unreliable. Reproducibility often depends on tribal knowledge rather than proper governance.
Teams often waste time fixing broken builds from unexpected updates or conflicts. They lack visibility into approved packages, security risks, and duplicates. Manual dependency tracking causes duplicated effort, inconsistent environments, and slow onboarding. Automation is minimal, meaning no vulnerability scanning, license checks, or centralized storage.
Decentralized approaches may seem initially flexible, but as development scales with more developers, larger codebases, and an increasing number of applications, teams experience increasing operational strain. They often duplicate efforts, adopt packages inconsistently, and lack shared standards, leading to delays, integration issues, and uneven quality. At this level, developers face unpredictable builds, last-minute firefighting, and unclear ownership of issues, making every day stressful and inefficient. As organizations grow, these gaps widen and become harder to manage, slowing delivery, increasing exposure, and threatening long-term maintainability. This doesn’t just cause friction; it creates real risk, delays releases, and weakens your organizations’ ability to scale.
In this article , we’ll examine the practical challenges organizations face when the foundational principles behind the five pillars are missing or poorly realized at a very basic level:
| Centralization | Without a single source of truth, time is lost searching, duplicating effort, and troubleshooting environment mismatches, leading to slower delivery and inconsistent outcomes. |
| Governance | Lack of policies and oversight enables shadow IT, unchecked compliance risks, and limited visibility into package usage. |
| Curation | Packages are adopted without review, increasing exposure to vulnerabilities, bugs, and costly rework. |
| Distribution | Opaque package flows complicate auditing, slow incident response, and break accountability. |
| Scalability | Fragmented tooling and ad hoc processes create bottlenecks that amplify complexity, reduce collaboration, and limit agility. |
Developer Enablement: Slowed Productivity from Fragmented Package Access
Due to a lack of a shared, trusted source for packages, developers often face inefficiencies and friction that slow down delivery.
⚠ Wasted time: Without a central repository, developers spend hours manually searching for, evaluating, and testing packages. This slows delivery, duplicates effort across teams, and takes focus away from higher-value development work.
⚠ Duplication and redundancy: When teams can’t see what others are doing, they often solve the same problems independently. Multiple teams might each build their own logging tools instead of sharing one solution, wasting time and resources. This leads to inconsistent solutions and fragments knowledge that could benefit everyone.
⚠ Inconsistent environments: Different package versions and setup practices cause bugs and integration issues. Some developers might update packages without coordination or configure environments inconsistently. This makes onboarding harder, troubleshooting longer, and wastes time fixing conflicts instead of delivering features.
⚠ Low trust and unclear standards: Without clear guidance on approved packages, developers rely on personal judgment. This increases the chance of using insecure or poor-quality dependencies and often leads to rework when problems arise.
⚠ Siloed knowledge: When teams don’t share successful tools, configurations or practices for using packages and managing dependencies, others miss out on proven solutions. This leads to duplicated effort, uneven practices, and slows learning and collaboration across the organization.
Without a centralized, trusted source for packages, development slows, risk increases, and teams waste effort solving the same problems in isolation, slowing down progress, reducing quality, and limiting the ability to scale effectively.
Security: Exposure to Vulnerable and Malicious Packages
Without controls in place, teams freely download packages from public sources with no safeguards against vulnerabilities or malicious code.
⚠ Exposure to vulnerable packages: The 2025 Black Duck report found that 86% of analyzed codebases contained vulnerable open-source components, with 81% of those having high- or critical-risk vulnerabilities. Using such components exposes your software to potential breaches, data loss, and costly remediation. Many of these vulnerabilities remain unpatched for years, increasing the risk of unexpected incidents that disrupt operations and damage trust.
⚠ Inconsistent security practices: According to a 2023 Snyk report, 60% of developers are unaware of vulnerabilities in the third-party code they use. This leads to uneven security across teams, leaving blind spots that increase breach risk, complicate risk management, and weaken the organization’s overall security posture.
⚠ Delayed detection and costly remediation – The average time to identify and contain a security breach is nearly 287 days, according to the 2024 IBM Cost of a Data Breach Report. Delays in fixing vulnerabilities can lead to increased remediation costs, operational disruptions, and greater reputational risk.
Without effective controls, organizations risk widespread exposure to vulnerable packages, inconsistent security practices, and delayed breach detection. These issues increase the likelihood of security incidents, drive up remediation costs, disrupt operations, and compromise trust in your software supply chain.
Governance: Lack of Policies Leads to Shadow IT and Noncompliance
Without enforced policies or standards, package usage becomes inconsistent and unmanaged, introducing serious operational and compliance risks.
⚠ Shadow IT emerges: Teams adopt tools and libraries independently, bypassing oversight and governance. This creates hidden security vulnerabilities, fragments workflows, and undermines operational consistency, putting projects and compliance at serious risk.
⚠ Noncompliance risk grows: Licensing, security, and regulatory requirements related to OSS packages are overlooked, exposing the organization to costly legal penalties and audit failures. These gaps put both the organization’s reputation and operations at serious risk.
⚠ Limited visibility and coordination: Management and security teams have little insight into package usage, making it difficult to enforce controls or track risks. This lack of transparency slows risk detection, fragments team efforts, and increases exposure to security and compliance failures.
⚠ Difficulty scaling governance: Without centralized standards, control weakens as teams and projects multiply. This fragmentation breeds inconsistent policies, heightens security and compliance risks, and strains operational resources.
Without shared policies and centralized governance, package management becomes fragmented and uncontrolled. This lack of oversight fuels shadow IT, escalates compliance risks, blinds management to critical vulnerabilities, and cripples the organization’s ability to scale securely and efficiently. Ultimately, unmanaged package usage threatens operational stability, legal compliance, and business growth.
Auditability: Lack of Visibility Complicates Compliance and Incident Response
When there’s no visibility into package usage, organizations struggle to respond quickly to security incidents or prove compliance during audits.
⚠ Limited incident response capability: Without timely and accurate data, teams struggle to quickly identify and remediate vulnerabilities. This delay increases exposure to security breaches, prolongs operational disruption, and amplifies risks across compliance, reputation, and financial stability.
⚠ Compliance audits become challenging: Incomplete or missing data hampers the ability to prove adherence to policies and regulations. This exposes the organization to audit failures, regulatory penalties, and erosion of stakeholder trust.
⚠ Absence of centralized logging: Without a single source of truth, teams can’t effectively track or report on package usage. This gap undermines visibility, weakens governance, and delays incident response, while making audits and accountability far more difficult.
⚠ Reduced accountability: Without clear visibility, ownership of packages and their associated risks becomes blurred. This lack of accountability delays response, allows risky dependencies to persist, and weakens governance across security and compliance.
When visibility is lacking, teams are left scrambling during incidents and audits, unable to answer what was used, who approved it, or where it went. The result is delayed response, compliance failures, and unmanaged risk that could have been prevented with proper oversight.
Scalability Readiness: Fragmented Workflows Strain Growth and Collaboration
Without standardized workflows, teams struggle to scale package management practices as the organization grows.
⚠ Tooling and version inconsistencies: When teams use different versions of the same package or rely on mismatched development tools, build systems, or runtime environments, the software delivery process becomes more error-prone and fragile. Time is lost resolving conflicts, onboarding slows, and the risk of security or compliance gaps increases.
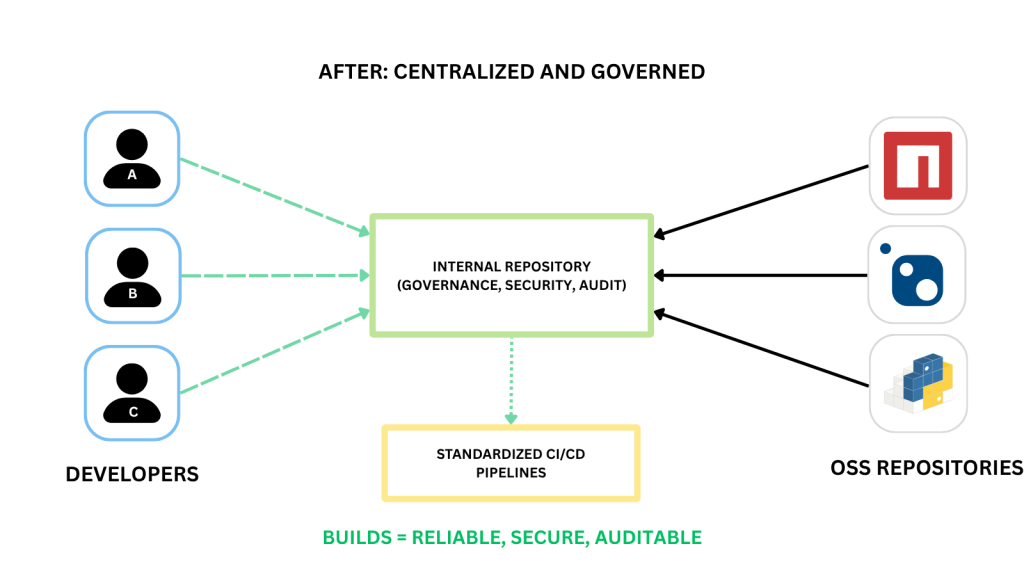
⚠ CI/CD becomes harder to manage: When each team takes a different approach, pipelines become harder to set up and maintain. Inconsistent package sourcing, like when developers pull directly from OSS sources, undermines reliability, security, and reproducibility. It leads to build failures, stalled automation, and scaling challenges.
⚠ Collaboration slows down: Instead of working toward shared solutions, teams spend time resolving differences in tools, processes, and assumptions. The result is duplicated effort, slower delivery, and inconsistent outcomes.
⚠ Scaling magnifies the problem: With more teams and projects, inconsistencies grow exponentially, creating greater friction and complexity. Lack of oversight leads to scattered tooling and diminished control over risk and compliance.

As teams and projects expand, inconsistent tooling, fragmented dependency management, and misaligned processes create operational friction that delays delivery, weakens collaboration, and increases security and compliance risks—challenges that only intensify without standardized workflows and centralized oversight.
Moving Forward: Leveling Up with Centralized Package Management
At this early stage of package management maturity, many enterprises face a common set of challenges: fragmented processes, inconsistent practices, and limited visibility. These issues not only slow down development but also increase operational risk, complicate scaling efforts, and require targeted actions to effectively overcome them.
✅ Centralization: The absence of a unified source of truth for packages leads to duplicated efforts, wasted time, and inconsistent environments. By implementing a centralized package repository like ProGet—with intelligent caching and a unified, shared catalog—teams can efficiently discover and share trusted packages without unnecessary duplication.
Why this helps: Centralization eliminates redundant work, speeds up development, and promotes consistency across teams—reducing integration issues and enhancing overall delivery quality.
✅ Governance: Without enforced policies, organizations risk the proliferation of shadow IT, unmanaged package usage, and compliance violations. Tools like ProGet provide role-based access controls, policy enforcement, and audit trails to ensure package usage adheres to organizational standards.
Why this helps: Strong governance minimizes security vulnerabilities and legal risks by restricting unauthorized package use, strengthening oversight, and enabling compliance with licensing and regulatory requirements.
✅ Curation: Adopting packages without review exposes software to vulnerabilities, bugs, and quality issues. ProGet’s approval workflows and built-in vulnerability scanning allow teams to vet and approve packages before adoption.
Why this helps: Effective curation reduces exposure to insecure or low-quality dependencies, preventing costly remediation and improving software reliability.
✅ Distribution: Opaque and inconsistent package distribution complicates incident response and auditing efforts. ProGet’s centralized logging, traceability, and metadata tracking provide full visibility into package flows across teams and systems.
Why this helps: Enhanced distribution visibility enables faster security incident resolution, smoother compliance audits, and clear accountability, strengthening operational resilience.
✅ Scalability: Fragmented tooling and processes become bottlenecks as organizations grow, impeding collaboration and build automation. ProGet supports scalable, standardized workflows, CI/CD integrations, and high-availability architectures to accommodate expanding teams and projects.
Why this helps: Preparing for scalability lays the groundwork for smoother growth, reliable builds, and dependable operations—enabling teams to stay aligned and maintain oversight as systems and demands grow more complex.
By moving beyond Level 1 and adopting a centralized, governed, curated, and scalable package management approach, organizations gain timely and accurate data that enables teams to quickly identify and remediate vulnerabilities. This unlocks faster delivery, stronger security, and greater operational confidence. Tools like ProGet provide a practical path forward, transforming package management from a source of risk and friction into a strategic enabler for sustainable software growth.
Are you a Level 1? Assess Your Position and Chart the Next Steps
Determining your organization’s package management maturity can be tricky when relying only on internal reviews. Blind spots, assumptions, and the absence of industry benchmarks often make it difficult to see the full picture. That’s why we recommend scheduling a guided assessment with our team. Our experts have worked across industries and can help surface risks and opportunities that are easy to miss from the inside.
You can schedule your assessment directly from our homepage:
Once complete, you’ll receive a detailed report that maps your current practices against our maturity model. The report provides both a high-level strategic view and level-specific chapters with practical next steps so you can confidently move forward.
In the meantime, if you haven’t checked it out yet, we also offer our Package Management at Scale guide as a free download. Inside, you’ll find the full collection of upcoming articles, plus deep dives into centralization, distribution, and curation. It also includes a hands-on rubric you can use right away to assess your team’s maturity. Download your copy today and get ahead of the curve.
